docs: general improvements and updates (#13485)
* docs: general improvements and updates * fix vale error
This commit is contained in:
@@ -14,6 +14,8 @@ The Medusa Admin dashboard is customizable, allowing you to add new pages, calle
|
||||
|
||||
For example, you can add a new page to show and manage product reviews, which aren't available natively in Medusa.
|
||||
|
||||
You can create a UI route directly in your Medusa application, or in a [plugin](../../plugins/page.mdx) if you want to share the UI route across multiple Medusa applications.
|
||||
|
||||
---
|
||||
|
||||
## How to Create a UI Route?
|
||||
|
||||
@@ -14,6 +14,8 @@ The Medusa Admin's pages are customizable for inserting widgets of custom conten
|
||||
|
||||
You create these widgets as React components that render the content and functionality of the widget.
|
||||
|
||||
You can create an admin widget directly in your Medusa application, or in a [plugin](../../plugins/page.mdx) if you want to share the widget across multiple Medusa applications.
|
||||
|
||||
---
|
||||
|
||||
## How to Create a Widget?
|
||||
|
||||
@@ -8,13 +8,19 @@ export const metadata = {
|
||||
|
||||
# {metadata.title}
|
||||
|
||||
In this document, you'll learn how to use the Auth Module's main service's methods to implement authentication flows and reset a user's password.
|
||||
In this guide, you'll learn how to use the methods of the Auth Module's service to implement authentication flows and reset a user's password.
|
||||
|
||||
<Note>
|
||||
|
||||
This guide is only recommended for complex cases, where you may need to heavily customize the authentication flows and need to use the Auth Module's service methods directly. For most use cases, you should use the [auth routes](../authentication-route/page.mdx) instead.
|
||||
|
||||
</Note>
|
||||
|
||||
## Authentication Methods
|
||||
|
||||
### Register
|
||||
|
||||
The [register method of the Auth Module's main service](/references/auth/register) creates an auth identity that can be authenticated later.
|
||||
The [register method of the Auth Module's service](/references/auth/register) creates an auth identity that can be authenticated later.
|
||||
|
||||
For example:
|
||||
|
||||
@@ -23,41 +29,83 @@ const data = await authModuleService.register(
|
||||
"emailpass",
|
||||
// passed to auth provider
|
||||
{
|
||||
// ...
|
||||
// pass data from request parameters, such as
|
||||
url: "example.com",
|
||||
headers: req.headers,
|
||||
query: req.query,
|
||||
// pass in the body the data necessary for the authentication provider
|
||||
// to register the user, such as email and password
|
||||
body: {
|
||||
email: "user@example.com",
|
||||
password: "supersecret",
|
||||
},
|
||||
protocol: req.protocol,
|
||||
}
|
||||
)
|
||||
```
|
||||
|
||||
This method calls the `register` method of the provider specified in the first parameter and returns its data.
|
||||
This method calls the `register` method of the provider specified in the first parameter. The method passes the second parameter as input for the provider, and returns its data.
|
||||
|
||||
Based on the returned data, you can determine if the registration was successful, and if any further action is required to complete the registration. This is explained further in the auth flows sections below.
|
||||
|
||||
### Authenticate
|
||||
|
||||
To authenticate a user, you use the [authenticate method of the Auth Module's main service](/references/auth/authenticate). For example:
|
||||
To authenticate or log in a user, you use the [authenticate method of the Auth Module's service](/references/auth/authenticate). For example:
|
||||
|
||||
```ts
|
||||
const data = await authModuleService.authenticate(
|
||||
"emailpass",
|
||||
// passed to auth provider
|
||||
{
|
||||
// ...
|
||||
// pass data from request parameters, such as
|
||||
url: "example.com",
|
||||
headers: req.headers,
|
||||
query: req.query,
|
||||
// pass in the body the data necessary for the authentication provider
|
||||
// to authenticate the user, such as email and password
|
||||
body: {
|
||||
email: "user@example.com",
|
||||
password: "supersecret",
|
||||
},
|
||||
protocol: req.protocol,
|
||||
}
|
||||
)
|
||||
```
|
||||
|
||||
This method calls the `authenticate` method of the provider specified in the first parameter and returns its data.
|
||||
This method calls the `authenticate` method of the provider specified in the first parameter. The method passes the second parameter as input for the provider, and returns its data.
|
||||
|
||||
Based on the returned data, you can determine if the authentication was successful, and if any further action is required to complete the authentication. This is explained further in the auth flows sections below.
|
||||
|
||||
---
|
||||
|
||||
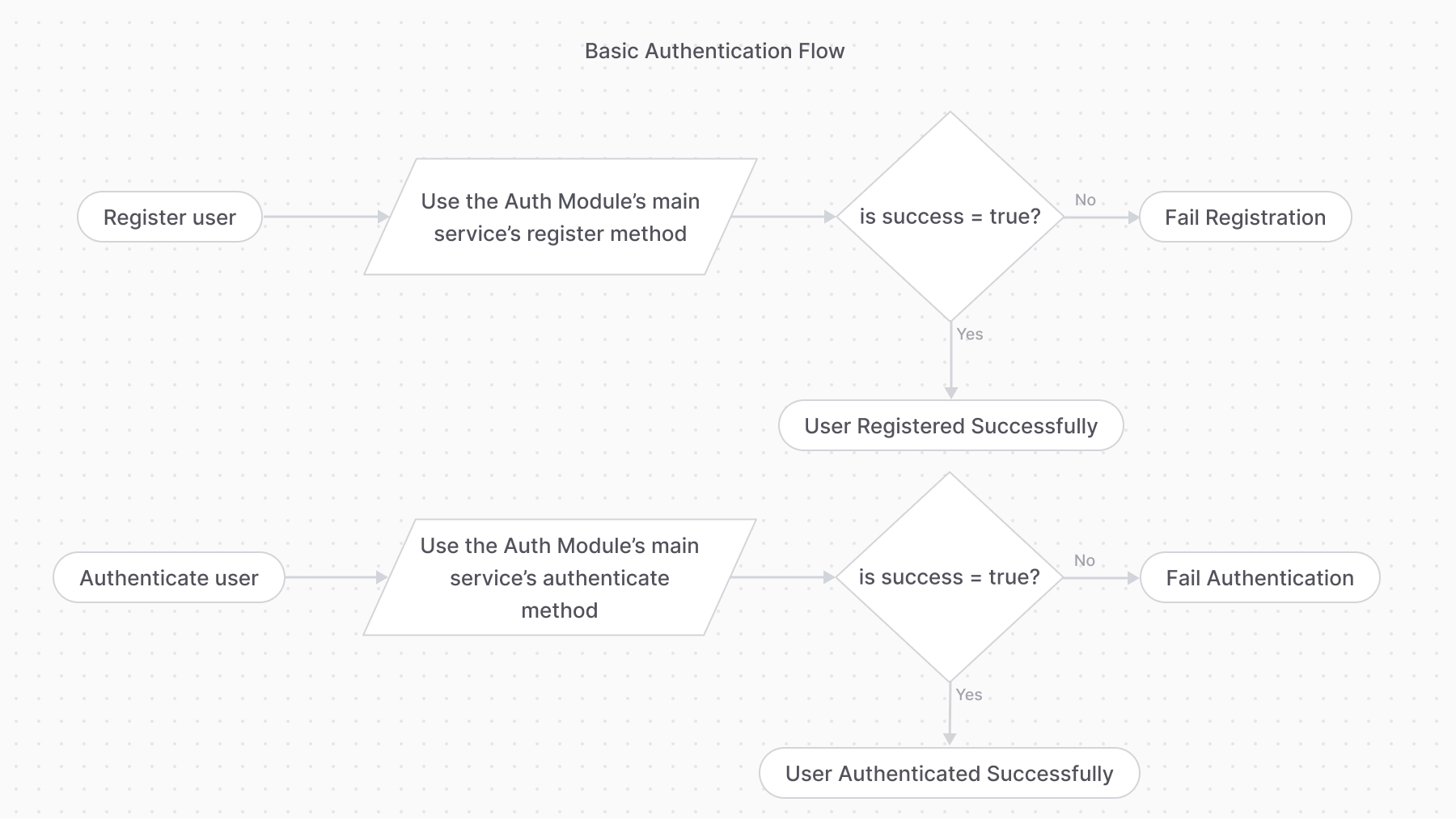
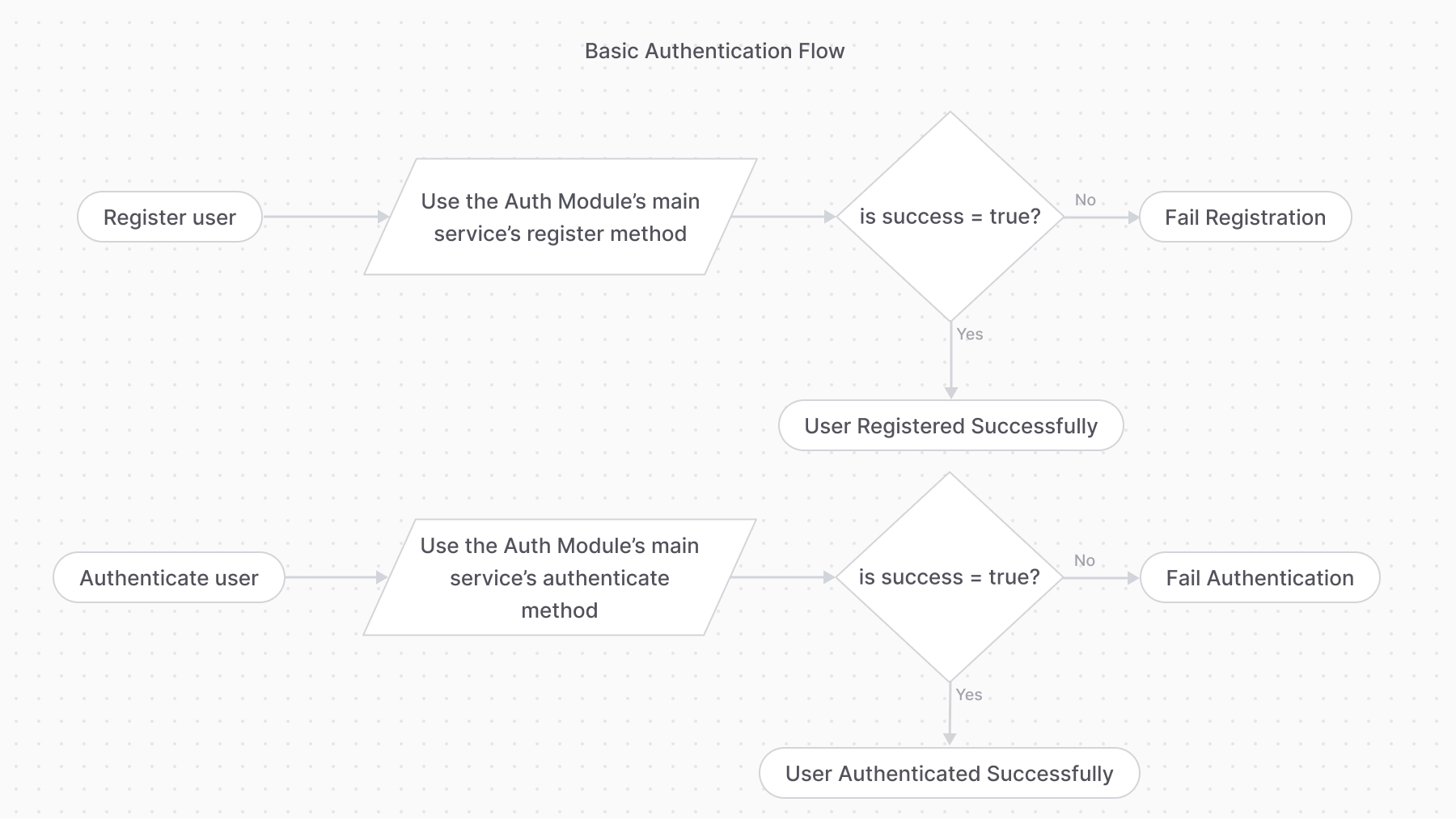
## Auth Flow 1: Basic Authentication
|
||||
|
||||
The basic authentication flow requires first using the `register` method, then the `authenticate` method:
|
||||
The basic authentication flow requires first using the `register` method, then the `authenticate` method.
|
||||
|
||||
|
||||
|
||||
### Step 1: Register User
|
||||
|
||||
```ts
|
||||
const { success, authIdentity, error } = await authModuleService.register(
|
||||
const {
|
||||
success,
|
||||
authIdentity,
|
||||
error
|
||||
} = await authModuleService.register(
|
||||
"emailpass",
|
||||
// passed to auth provider
|
||||
{
|
||||
// ...
|
||||
// pass data from request parameters, such as
|
||||
url: "example.com",
|
||||
headers: req.headers,
|
||||
query: req.query,
|
||||
// pass in the body the data necessary for the authentication provider
|
||||
// to register the user, such as email and password
|
||||
body: {
|
||||
email: "user@example.com",
|
||||
password: "supersecret",
|
||||
},
|
||||
protocol: req.protocol,
|
||||
}
|
||||
)
|
||||
|
||||
@@ -66,13 +114,50 @@ if (error) {
|
||||
// TODO return an error
|
||||
return
|
||||
}
|
||||
```
|
||||
|
||||
// later (can be another route for log-in)
|
||||
const { success, authIdentity, location } = await authModuleService.authenticate(
|
||||
If the `register` method returns an `error` property, the registration failed, and you can return an error message to the user.
|
||||
|
||||
Otherwise, if the `success` property is `true`, the registration was successful, and the user's authentication details are available within the `authIdentity` object.
|
||||
|
||||
<Note>
|
||||
|
||||
Check out the [AuthIdentity](/references/auth/models/AuthIdentity) reference for the received properties in `authIdentity`.
|
||||
|
||||
</Note>
|
||||
|
||||
#### Registering Auth Identities with Same Identifier
|
||||
|
||||
If an auth identity, such as a `customer`, tries to register with an email of another auth identity, the `register` method returns an error. This can happen either if another customer is using the same email, or an admin user has the same email.
|
||||
|
||||
There are two ways to handle this:
|
||||
|
||||
- Consider the customer authenticated if the `authenticate` method validates that the email and password are correct. This allows admin users, for example, to authenticate as customers.
|
||||
- Return an error message to the customer, informing them that the email is already in use.
|
||||
|
||||
### Step 2: Authenticate User
|
||||
|
||||
```ts
|
||||
// later (can be another route for login)
|
||||
const {
|
||||
success,
|
||||
authIdentity,
|
||||
location
|
||||
} = await authModuleService.authenticate(
|
||||
"emailpass",
|
||||
// passed to auth provider
|
||||
{
|
||||
// ...
|
||||
// pass data from request parameters, such as
|
||||
url: "example.com",
|
||||
headers: req.headers,
|
||||
query: req.query,
|
||||
// pass in the body the data necessary for the authentication provider
|
||||
// to authenticate the user, such as email and password
|
||||
body: {
|
||||
email: "user@example.com",
|
||||
password: "supersecret",
|
||||
},
|
||||
protocol: req.protocol,
|
||||
}
|
||||
)
|
||||
|
||||
@@ -81,26 +166,9 @@ if (success && !location) {
|
||||
}
|
||||
```
|
||||
|
||||
If `success` is true and `location` isn't set, the user is authenticated successfully, and their authentication details are available within the `authIdentity` object.
|
||||
If the `authenticate` method returns a `success` property that is `true`, and the `location` property is not set, the user is authenticated successfully. Their authentication details are available within the `authIdentity` object.
|
||||
|
||||
The next section explains the flow if `location` is set.
|
||||
|
||||
<Note>
|
||||
|
||||
Check out the [AuthIdentity](/references/auth/models/AuthIdentity) reference for the received properties in `authIdentity`.
|
||||
|
||||
</Note>
|
||||
|
||||
|
||||
|
||||
### Auth Identity with Same Identifier
|
||||
|
||||
If an auth identity, such as a `customer`, tries to register with an email of another auth identity, the `register` method returns an error. This can happen either if another customer is using the same email, or an admin user has the same email.
|
||||
|
||||
There are two ways to handle this:
|
||||
|
||||
- Consider the customer authenticated if the `authenticate` method validates that the email and password are correct. This allows admin users, for example, to authenticate as customers.
|
||||
- Return an error message to the customer, informing them that the email is already in use.
|
||||
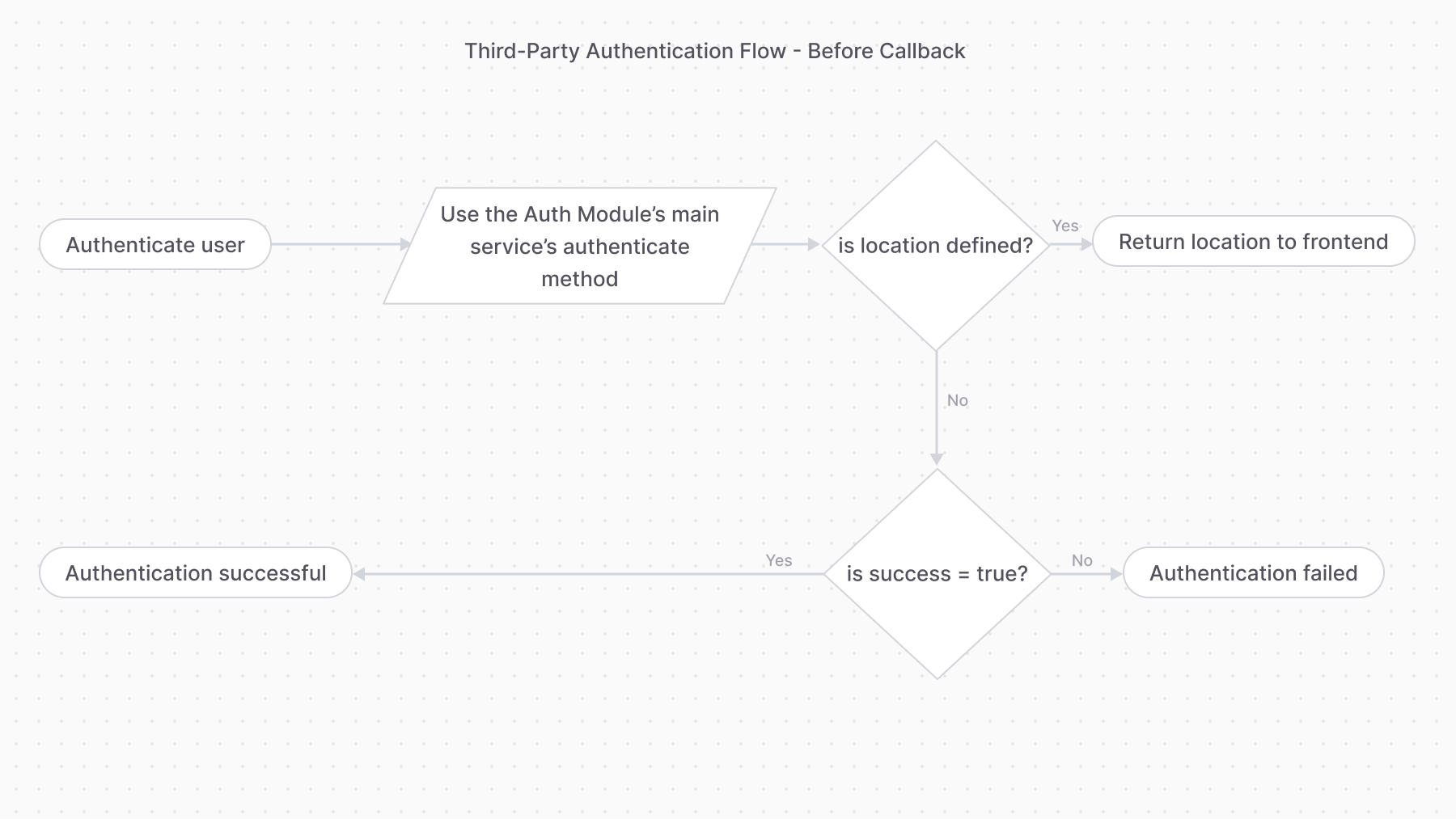
Otherwise, if the `location` property is set, you must follow the [third-party service authentication flow](#auth-flow-2-third-party-service-authentication) to complete the authentication.
|
||||
|
||||
---
|
||||
|
||||
@@ -113,12 +181,17 @@ const { success, authIdentity, location } = await authModuleService.authenticate
|
||||
"google",
|
||||
// passed to auth provider
|
||||
{
|
||||
// ...
|
||||
// pass data from request parameters, such as
|
||||
url: "example.com",
|
||||
headers: req.headers,
|
||||
query: req.query,
|
||||
body: req.body,
|
||||
protocol: req.protocol,
|
||||
}
|
||||
)
|
||||
|
||||
if (location) {
|
||||
// return the location for the front-end to redirect to
|
||||
// return the location for the frontend to redirect to
|
||||
}
|
||||
|
||||
if (!success) {
|
||||
@@ -128,18 +201,22 @@ if (!success) {
|
||||
// authentication successful
|
||||
```
|
||||
|
||||
If the `authenticate` method returns a `location` property, the authentication process requires the user to perform an action with a third-party service. So, you return the `location` to the front-end or client to redirect to that URL.
|
||||
If the `authenticate` method returns a `location` property, the authentication process requires the user to perform an action with a third-party service. So, you return the `location` to the frontend or client to redirect to that URL.
|
||||
|
||||
For example, when using the `google` provider, the `location` is the URL that the user is navigated to login.
|
||||
For example, when using the `google` provider, the `location` is the URL that the user must be redirected to in order to log in with their Google account.
|
||||
|
||||
|
||||
|
||||
### Overriding Callback URL
|
||||
|
||||
The Google and GitHub providers allow you to override their `callbackUrl` option during authentication. This is useful when you redirect the user after authentication to a URL based on its actor type. For example, you redirect admin users and customers to different pages.
|
||||
The Google and GitHub providers allow you to override their `callbackUrl` option during authentication. This is useful when you redirect the user after authentication to a URL based on their actor type. For example, you redirect admin users and customers to different pages.
|
||||
|
||||
```ts
|
||||
const { success, authIdentity, location } = await authModuleService.authenticate(
|
||||
const {
|
||||
success,
|
||||
authIdentity,
|
||||
location
|
||||
} = await authModuleService.authenticate(
|
||||
"google",
|
||||
// passed to auth provider
|
||||
{
|
||||
@@ -153,7 +230,7 @@ const { success, authIdentity, location } = await authModuleService.authenticate
|
||||
|
||||
Providers handling this authentication flow must implement the `validateCallback` method. It implements the logic to validate the authentication with the third-party service.
|
||||
|
||||
So, once the user performs the required action with the third-party service (for example, log-in with Google), the frontend must redirect to an API route that uses the [validateCallback method of the Auth Module's main service](/references/auth/validateCallback).
|
||||
So, once the user performs the required action with the third-party service (for example, log in with Google), the frontend must redirect to an API route that uses the [validateCallback method of the Auth Module's service](/references/auth/validateCallback).
|
||||
|
||||
The method calls the specified provider’s `validateCallback` method passing it the authentication details it received in the second parameter:
|
||||
|
||||
@@ -190,7 +267,7 @@ If the returned `success` property is `true`, the authentication with the third-
|
||||
|
||||
## Reset Password
|
||||
|
||||
To update a user's password or other authentication details, use the `updateProvider` method of the Auth Module's main service. It calls the `update` method of the specified authentication provider.
|
||||
To update a user's password or other authentication details, use the [updateProvider method of the Auth Module's service](/references/auth/updateProvider). It calls the `update` method of the specified authentication provider.
|
||||
|
||||
For example:
|
||||
|
||||
@@ -211,6 +288,6 @@ if (success) {
|
||||
|
||||
The method accepts as a first parameter the ID of the provider, and as a second parameter the data necessary to reset the password.
|
||||
|
||||
In the example above, you use the `emailpass` provider, so you have to pass an object having an `email` and `password` properties.
|
||||
In the example above, you use the `emailpass` provider, so you have to pass an object having `entity_id` and `password` properties.
|
||||
|
||||
If the returned `success` property is `true`, the password has reset successfully.
|
||||
If the returned `success` property is `true`, the password has been reset successfully.
|
||||
@@ -4,13 +4,13 @@ export const metadata = {
|
||||
|
||||
# {metadata.title}
|
||||
|
||||
In this document, you’ll learn about concepts related to identity and actors in the Auth Module.
|
||||
In this guide, you’ll learn about concepts related to identity and actors in the Auth Module.
|
||||
|
||||
## What is an Auth Identity?
|
||||
|
||||
The [AuthIdentity data model](/references/auth/models/AuthIdentity) represents a user registered by an [authentication provider](../auth-providers/page.mdx). When a user is registered using an authentication provider, the provider creates a record of `AuthIdentity`.
|
||||
|
||||
Then, when the user logs-in in the future with the same authentication provider, the associated auth identity is used to validate their credentials.
|
||||
Then, when the user logs in with the same authentication provider, the associated auth identity is used to validate their credentials.
|
||||
|
||||
---
|
||||
|
||||
@@ -18,7 +18,7 @@ Then, when the user logs-in in the future with the same authentication provider,
|
||||
|
||||
An actor type is a type of user that can be authenticated. The Auth Module doesn't store or manage any user-like models, such as for customers or users. Instead, the user types are created and managed by other modules. For example, a customer is managed by the [Customer Module](../../customer/page.mdx).
|
||||
|
||||
Then, when an auth identity is created for the actor type, the ID of the user is stored in the `app_metadata` property of the auth identity.
|
||||
When an auth identity is created for an actor type, the ID of the user is stored in the `app_metadata` property of the auth identity.
|
||||
|
||||
For example, an auth identity of a customer has the following `app_metadata` property:
|
||||
|
||||
@@ -36,7 +36,7 @@ The ID of the user is stored in the key `{actor_type}_id` of the `app_metadata`
|
||||
|
||||
## Protect Routes by Actor Type
|
||||
|
||||
When you protect routes with the `authenticate` middleware, you specify in its first parameter the actor type that must be authenticated to access the specified API routes.
|
||||
When you protect routes with the [authenticate middleware](!docs!/learn/fundamentals/api-routes/protected-routes), you specify in its first parameter the actor type that must be authenticated to access the API routes.
|
||||
|
||||
For example:
|
||||
|
||||
@@ -68,8 +68,8 @@ By specifying `user` as the first parameter of `authenticate`, only authenticate
|
||||
|
||||
## Custom Actor Types
|
||||
|
||||
You can define custom actor types that allows a custom user, managed by your custom module, to authenticate into Medusa.
|
||||
You can define custom actor types that allow a custom user, managed by your custom module, to authenticate into Medusa.
|
||||
|
||||
For example, if you have a custom module with a `Manager` data model, you can authenticate managers with the `manager` actor type.
|
||||
|
||||
Learn how to create a custom actor type in [this guide](../create-actor-type/page.mdx).
|
||||
Learn how to create a custom actor type in the [Create Manager Actor Type guide](../create-actor-type/page.mdx).
|
||||
@@ -6,17 +6,15 @@ export const metadata = {
|
||||
|
||||
# {metadata.title}
|
||||
|
||||
In this document, you’ll learn about the Emailpass auth module provider and how to install and use it in the Auth Module.
|
||||
In this guide, you’ll learn about the Emailpass Auth Module Provider and how to configure it.
|
||||
|
||||
Using the Emailpass auth module provider, you allow users to register and login with an email and password.
|
||||
|
||||
---
|
||||
By using the Emailpass Auth Module Provider, you allow users to register and log in with an email and password.
|
||||
|
||||
## Register the Emailpass Auth Module Provider
|
||||
|
||||
The Emailpass auth provider is registered by default with the Auth Module.
|
||||
The Emailpass Auth Module Provider is registered by default with the Auth Module.
|
||||
|
||||
If you want to pass options to the provider, add the provider to the `providers` option of the Auth Module:
|
||||
If you want to pass options to the provider, add the provider to the `providers` option of the Auth Module in your `medusa-config.ts`:
|
||||
|
||||
```ts title="medusa-config.ts"
|
||||
import { Modules, ContainerRegistrationKeys } from "@medusajs/framework/utils"
|
||||
@@ -66,7 +64,7 @@ module.exports = defineConfig({
|
||||
</Table.Cell>
|
||||
<Table.Cell>
|
||||
|
||||
An object of configurations to use when hashing the user's
|
||||
An object of configurations for hashing the user's
|
||||
password. Refer to [scrypt-kdf](https://www.npmjs.com/package/scrypt-kdf#-hash)'s
|
||||
documentation for accepted options.
|
||||
|
||||
|
||||
@@ -6,24 +6,16 @@ export const metadata = {
|
||||
|
||||
# {metadata.title}
|
||||
|
||||
In this document, you’ll learn about the GitHub Auth Module Provider and how to install and use it in the Auth Module.
|
||||
In this guide, you’ll learn about the GitHub Auth Module Provider and how to configure it.
|
||||
|
||||
The Github Auth Module Provider authenticates users with their GitHub account.
|
||||
The GitHub Auth Module Provider allows you to authenticate users with their GitHub account.
|
||||
|
||||
<Note title="Tip">
|
||||
|
||||
Learn about the authentication flow in [this guide](../../authentication-route/page.mdx).
|
||||
|
||||
</Note>
|
||||
|
||||
---
|
||||
|
||||
## Register the Github Auth Module Provider
|
||||
## Register the GitHub Auth Module Provider
|
||||
|
||||
<Prerequisites
|
||||
items={[
|
||||
{
|
||||
text: "Register GitHub App. When setting the Callback URL, set it to a URL in your frontend that later uses Medusa's callback route to validate the authentication.",
|
||||
text: "Register a GitHub App. When setting the Callback URL, set it to a URL in your frontend that later uses Medusa's callback route to validate the authentication.",
|
||||
link: "https://docs.github.com/en/apps/creating-github-apps/setting-up-a-github-app/creating-a-github-app"
|
||||
},
|
||||
{
|
||||
@@ -33,7 +25,7 @@ Learn about the authentication flow in [this guide](../../authentication-route/p
|
||||
]}
|
||||
/>
|
||||
|
||||
Add the module to the array of providers passed to the Auth Module:
|
||||
To use the GitHub Auth Module Provider, add the module to the array of providers passed to the Auth Module in your `medusa-config.ts`:
|
||||
|
||||
```ts title="medusa-config.ts"
|
||||
import { Modules, ContainerRegistrationKeys } from "@medusajs/framework/utils"
|
||||
@@ -146,12 +138,12 @@ GITHUB_CALLBACK_URL=<YOUR_GITHUB_CALLBACK_URL>
|
||||
|
||||
## Override Callback URL During Authentication
|
||||
|
||||
In many cases, you may have different callback URL for actor types. For example, you may redirect admin users to a different URL than customers after authentication.
|
||||
In many cases, you may have different callback URLs for actor types. For example, you may redirect admin users to a different URL than customers after authentication.
|
||||
|
||||
The [Authenticate or Login API Route](../../authentication-route/page.mdx#login-route) can accept a `callback_url` body parameter to override the provider's `callbackUrl` option. Learn more in [this documentation](../../authentication-route/page.mdx#login-route).
|
||||
The [Authenticate or Login API Route](../../authentication-route/page.mdx#login-route) accepts a `callback_url` body parameter to override the provider's `callbackUrl` option. Learn more in the [Auth Flows with Routes guide](../../authentication-route/page.mdx#login-route).
|
||||
|
||||
---
|
||||
|
||||
## Examples
|
||||
|
||||
- [How to implement third-party / social login in the storefront.](../../../../storefront-development/customers/third-party-login/page.mdx).
|
||||
- [How to implement third-party / social login in the storefront](../../../../storefront-development/customers/third-party-login/page.mdx)
|
||||
|
||||
@@ -6,17 +6,9 @@ export const metadata = {
|
||||
|
||||
# {metadata.title}
|
||||
|
||||
In this document, you’ll learn about the Google Auth Module Provider and how to install and use it in the Auth Module.
|
||||
In this guide, you’ll learn about the Google Auth Module Provider and how to install and use it in the Auth Module.
|
||||
|
||||
The Google Auth Module Provider authenticates users with their Google account.
|
||||
|
||||
<Note title="Tip">
|
||||
|
||||
Learn about the authentication flow for third-party providers in [this guide](../../authentication-route/page.mdx#2-third-party-service-authenticate-flow).
|
||||
|
||||
</Note>
|
||||
|
||||
---
|
||||
The Google Auth Module Provider allows you to authenticate users with their Google account.
|
||||
|
||||
## Register the Google Auth Module Provider
|
||||
|
||||
@@ -33,7 +25,7 @@ Learn about the authentication flow for third-party providers in [this guide](..
|
||||
]}
|
||||
/>
|
||||
|
||||
Add the module to the array of providers passed to the Auth Module:
|
||||
To use the Google Auth Module Provider, add the module to the array of providers passed to the Auth Module in your `medusa-config.ts`:
|
||||
|
||||
```ts title="medusa-config.ts"
|
||||
import { Modules, ContainerRegistrationKeys } from "@medusajs/framework/utils"
|
||||
@@ -147,11 +139,9 @@ GOOGLE_CALLBACK_URL=<YOUR_GOOGLE_CALLBACK_URL>
|
||||
|
||||
---
|
||||
|
||||
---
|
||||
|
||||
## Override Callback URL During Authentication
|
||||
|
||||
In many cases, you may have different callback URL for actor types. For example, you may redirect admin users to a different URL than customers after authentication.
|
||||
In many cases, you may have different callback URLs for actor types. For example, you may redirect admin users to a different URL than customers after authentication.
|
||||
|
||||
The [Authenticate or Login API Route](../../authentication-route/page.mdx#login-route) can accept a `callback_url` body parameter to override the provider's `callbackUrl` option. Learn more in [this documentation](../../authentication-route/page.mdx#login-route).
|
||||
|
||||
@@ -159,4 +149,4 @@ The [Authenticate or Login API Route](../../authentication-route/page.mdx#login-
|
||||
|
||||
## Examples
|
||||
|
||||
- [How to implement Google social login in the storefront](../../../../storefront-development/customers/third-party-login/page.mdx).
|
||||
- [How to implement Google social login in the storefront](../../../../storefront-development/customers/third-party-login/page.mdx)
|
||||
|
||||
@@ -4,11 +4,11 @@ export const metadata = {
|
||||
|
||||
# {metadata.title}
|
||||
|
||||
This document explains how the Inventory Module is used within the Medusa application's flows.
|
||||
In this guide, you'll learn how Medusa uses the Inventory Module in its commerce flows, including product variant creation, adding to cart, order placement, order fulfillment, and order return.
|
||||
|
||||
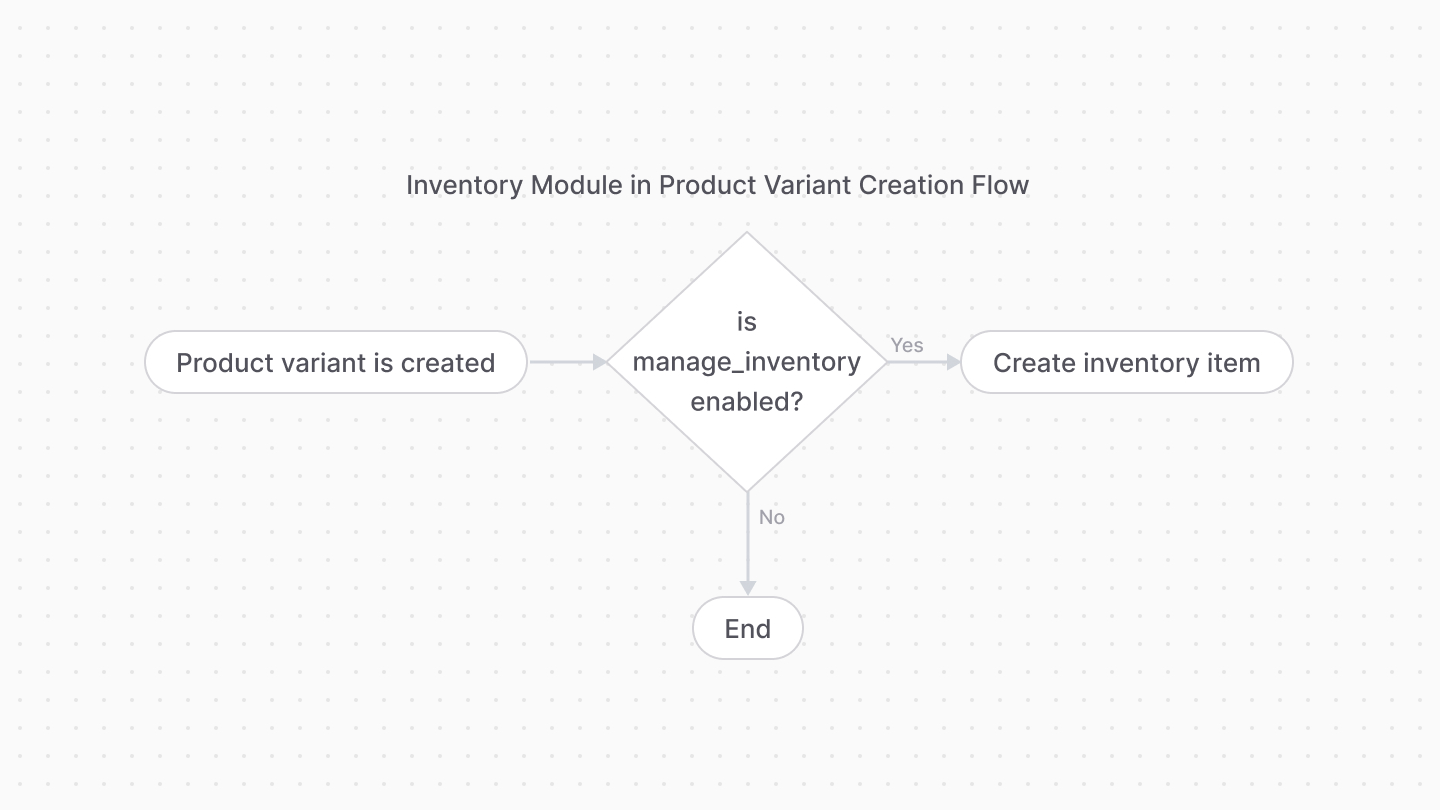
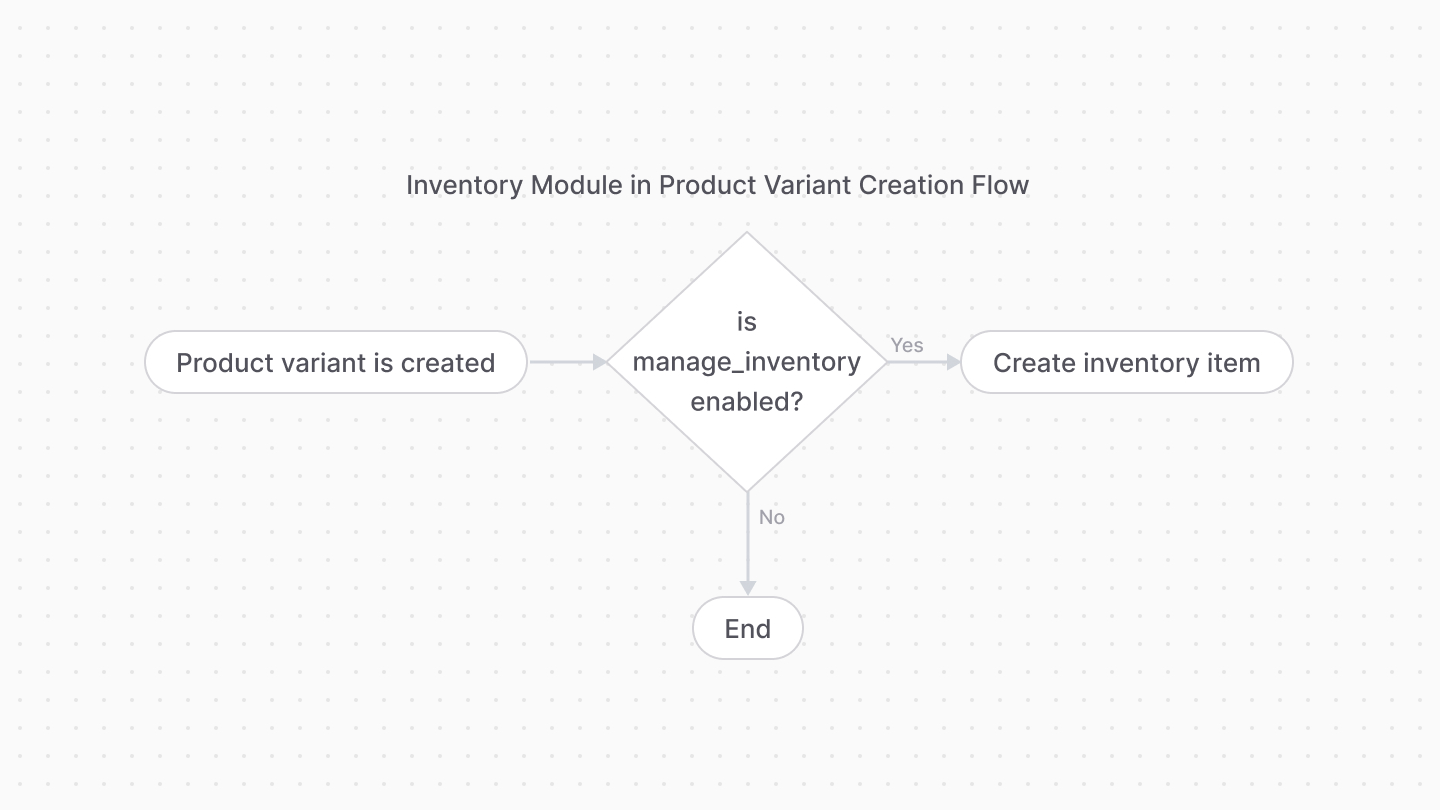
## Product Variant Creation
|
||||
|
||||
When a product variant is created and its `manage_inventory` property's value is `true`, the Medusa application creates an inventory item associated with that product variant.
|
||||
When a product variant is created and its `manage_inventory` property's value is `true` and the variant's `inventory_items` are set, the Medusa application creates an inventory item associated with that product variant.
|
||||
|
||||
<Note title="Tip">
|
||||
|
||||
@@ -16,13 +16,13 @@ This flow is implemented within the [createProductVariantsWorkflow](/references/
|
||||
|
||||
</Note>
|
||||
|
||||
|
||||
|
||||
|
||||
---
|
||||
|
||||
## Add to Cart
|
||||
|
||||
When a product variant with `manage_inventory` set to `true` is added to cart, the Medusa application checks whether there's sufficient stocked quantity. If not, an error is thrown and the product variant won't be added to the cart.
|
||||
When a product variant with `manage_inventory` set to `true` is added to the cart, the Medusa application checks whether there's sufficient stocked quantity. If not, an error is thrown and the product variant won't be added to the cart.
|
||||
|
||||
<Note title="Tip">
|
||||
|
||||
@@ -34,7 +34,7 @@ This flow is implemented within the [addToCartWorkflow](/references/medusa-workf
|
||||
|
||||
---
|
||||
|
||||
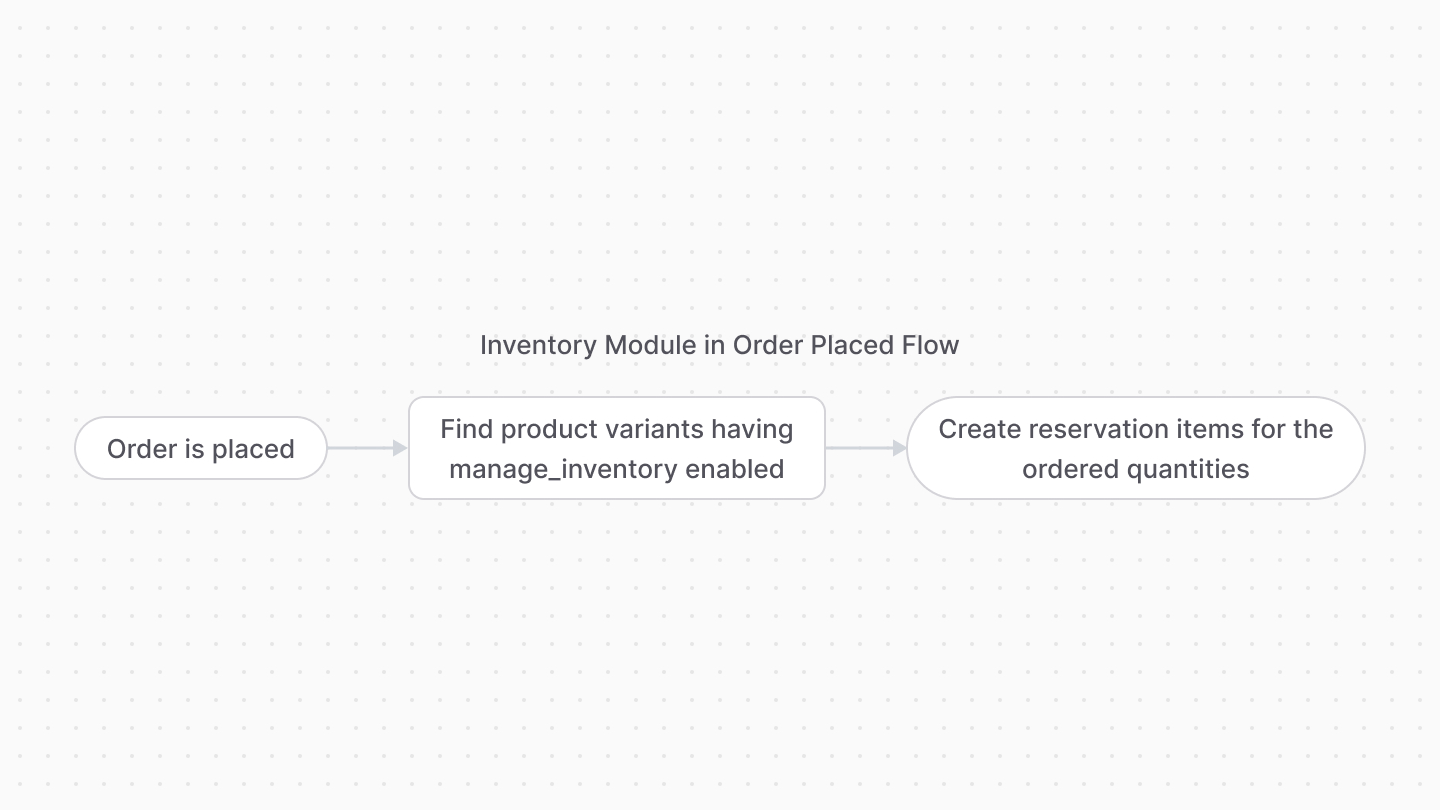
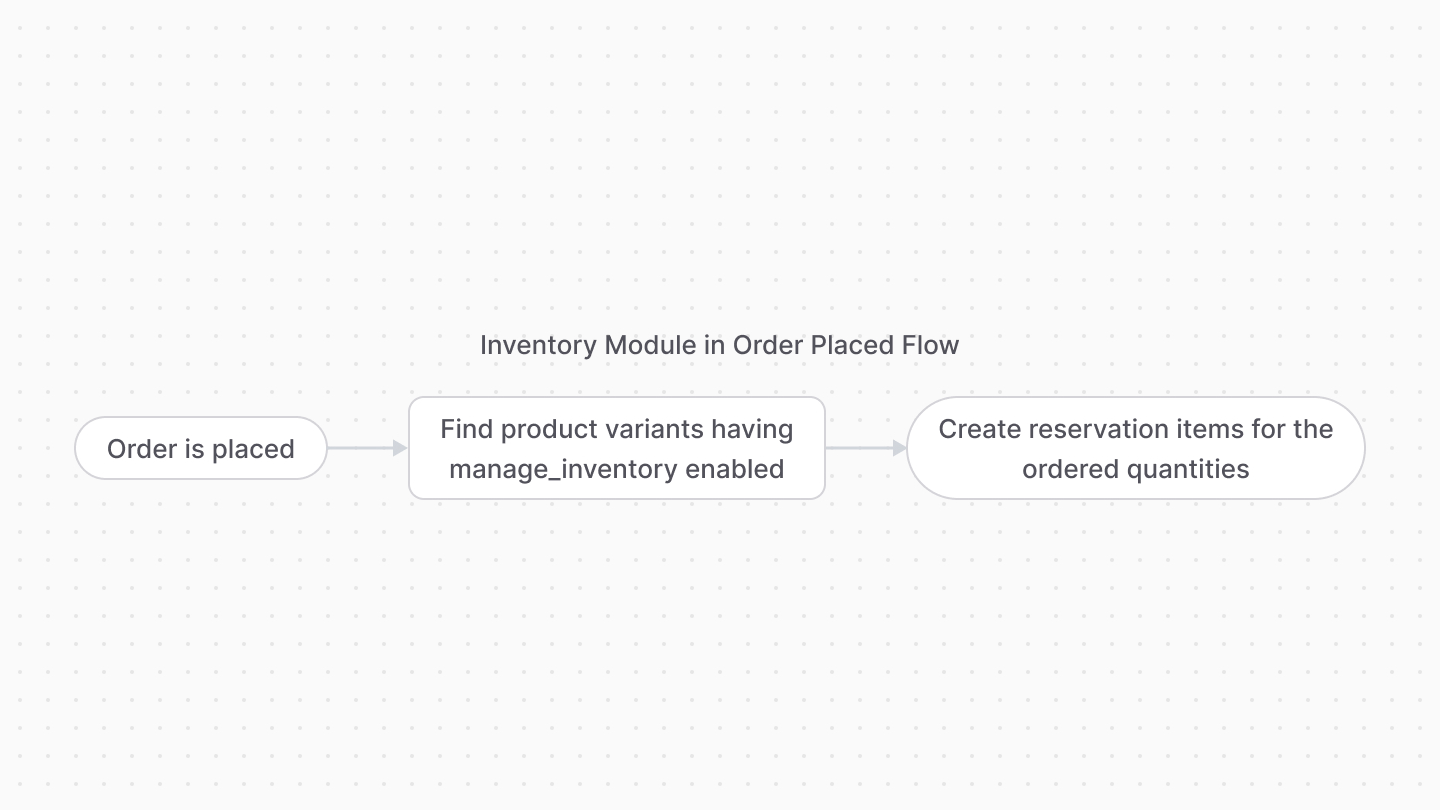
## Order Placed
|
||||
## Order is Placed
|
||||
|
||||
When an order is placed, the Medusa application creates a reservation item for each product variant with `manage_inventory` set to `true`.
|
||||
|
||||
@@ -44,7 +44,7 @@ This flow is implemented within the [completeCartWorkflow](/references/medusa-wo
|
||||
|
||||
</Note>
|
||||
|
||||
|
||||
|
||||
|
||||
---
|
||||
|
||||
|
||||
@@ -11,11 +11,11 @@ export const metadata = {
|
||||
|
||||
# {metadata.title}
|
||||
|
||||
Commands starting with `db:` perform actions on the database.
|
||||
Commands in the Medusa CLI starting with `db:` perform actions on the database.
|
||||
|
||||
## db\:setup
|
||||
|
||||
Creates a database for the Medusa application with the specified name, if it doesn't exit. Then, it runs migrations and syncs links.
|
||||
Creates a database for the Medusa application with the specified name, if it doesn't exist. Then, it runs migrations and syncs links.
|
||||
|
||||
It also updates your `.env` file with the database name.
|
||||
|
||||
@@ -158,7 +158,7 @@ Use this command if you're setting up a Medusa project or database manually.
|
||||
|
||||
## db\:create
|
||||
|
||||
Creates a database for the Medusa application with the specified name, if it doesn't exit.
|
||||
Creates a database for the Medusa application with the specified name, if it doesn't exist.
|
||||
|
||||
It also updates your `.env` file with the database name.
|
||||
|
||||
@@ -260,7 +260,7 @@ npx medusa db:generate <module_names...>
|
||||
</Table.Cell>
|
||||
<Table.Cell>
|
||||
|
||||
The name of one or more module (separated by spaces) to generate migrations for. For example, `helloModuleService`.
|
||||
The name of one or more modules (separated by spaces) to generate migrations for. For example, `brand`.
|
||||
|
||||
</Table.Cell>
|
||||
<Table.Cell>
|
||||
@@ -397,7 +397,7 @@ Use this command if you've updated the Medusa packages, or you've created custom
|
||||
|
||||
## db\:rollback
|
||||
|
||||
Revert the last migrations ran on one or more modules.
|
||||
Revert the last migrations run on one or more modules.
|
||||
|
||||
```bash
|
||||
npx medusa db:rollback <module_names...>
|
||||
@@ -422,7 +422,7 @@ npx medusa db:rollback <module_names...>
|
||||
</Table.Cell>
|
||||
<Table.Cell>
|
||||
|
||||
The name of one or more module (separated by spaces) to rollback their migrations for. For example, `helloModuleService`.
|
||||
The name of one or more modules (separated by spaces) to rollback their migrations for. For example, `brand`.
|
||||
|
||||
</Table.Cell>
|
||||
<Table.Cell>
|
||||
|
||||
@@ -11,7 +11,7 @@ export const metadata = {
|
||||
|
||||
# {metadata.title}
|
||||
|
||||
Run a custom CLI script. Learn more about it in [this guide](!docs!/learn/fundamentals/custom-cli-scripts).
|
||||
Run a custom CLI script using Medusa's CLI tool. Learn more about it in [Custom CLI Scripts guide](!docs!/learn/fundamentals/custom-cli-scripts).
|
||||
|
||||
```bash
|
||||
npx medusa exec [file] [args...]
|
||||
@@ -36,7 +36,7 @@ npx medusa exec [file] [args...]
|
||||
</Table.Cell>
|
||||
<Table.Cell>
|
||||
|
||||
The path to the TypeScript or JavaScript file holding the function to execute.
|
||||
The path to the TypeScript or JavaScript file containing the function to execute.
|
||||
|
||||
</Table.Cell>
|
||||
<Table.Cell>
|
||||
|
||||
@@ -11,7 +11,7 @@ export const metadata = {
|
||||
|
||||
# {metadata.title}
|
||||
|
||||
Commands starting with `plugin:` perform actions related to [plugin](!docs!/learn/fundamentals/plugins) development.
|
||||
Commands in the Medusa CLI starting with `plugin:` perform actions related to [plugin development](!docs!/learn/fundamentals/plugins).
|
||||
|
||||
<Note>
|
||||
|
||||
@@ -92,7 +92,7 @@ npx medusa plugin:db:generate
|
||||
|
||||
## plugin\:build
|
||||
|
||||
Build a plugin before publishing it to NPM. The command will compile an output in the `.medusa/server` directory.
|
||||
Build a plugin before publishing it to NPM. The command will compile the output in the `.medusa/server` directory.
|
||||
|
||||
```bash
|
||||
npx medusa plugin:build
|
||||
|
||||
@@ -11,7 +11,7 @@ export const metadata = {
|
||||
|
||||
# {metadata.title}
|
||||
|
||||
Enable or disable the collection of anonymous data usage. If no option is provided, the command enables the collection of anonymous data usage.
|
||||
Enable or disable the collection of anonymous usage data. If no option is provided, the command enables the collection of anonymous usage data.
|
||||
|
||||
```bash
|
||||
npx medusa telemetry
|
||||
|
||||
Reference in New Issue
Block a user